Claude Mythos Preview should be taken seriously, but the cleanest reading of the public evidence is less dramatic than “only Mythos can do this.” It looks like a leading frontier model for complex cyber work, especially when used as an agent with tools and network access. That is different from proving that its cybersecurity reasoning is unavailable in cheaper public models.
The short verdict
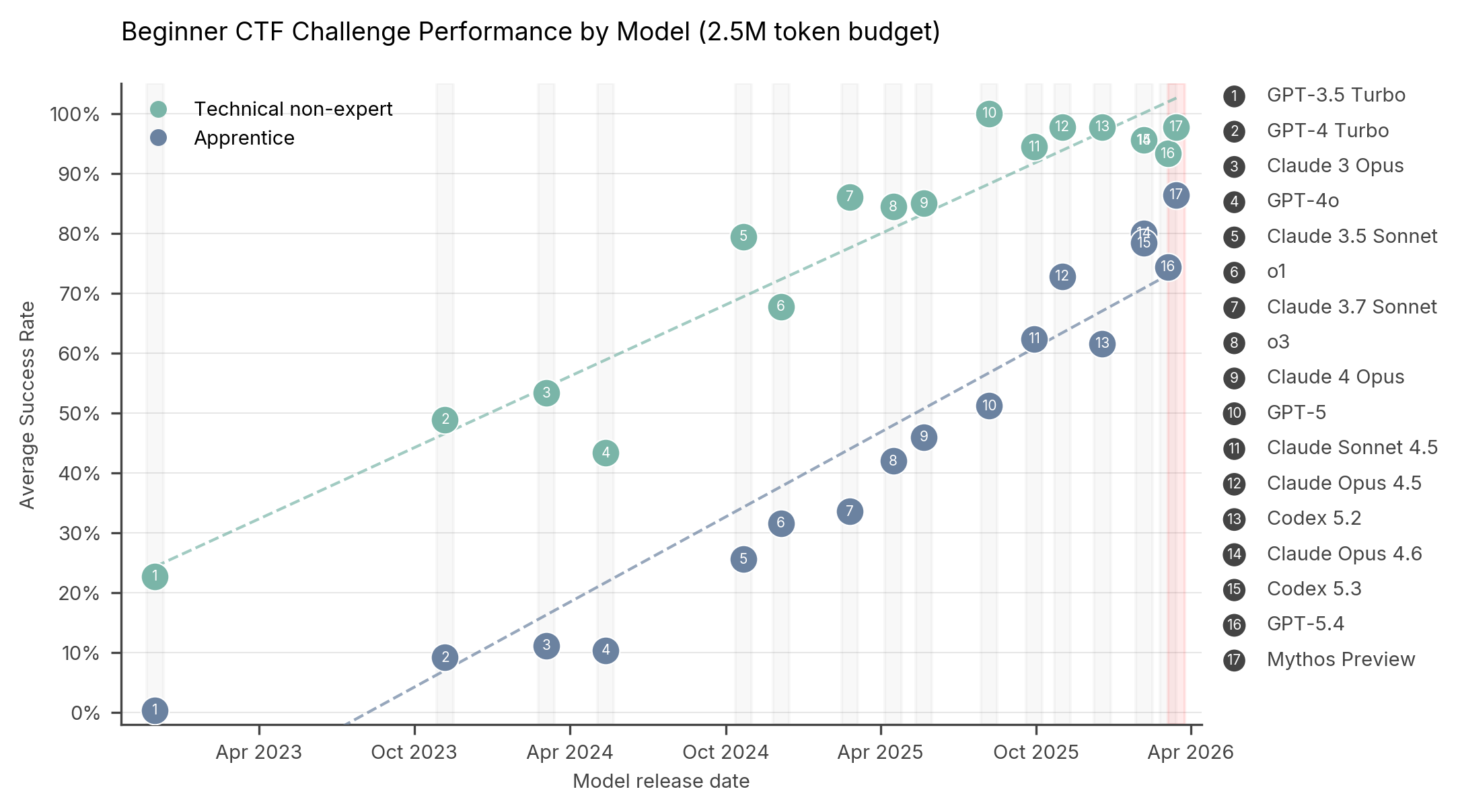
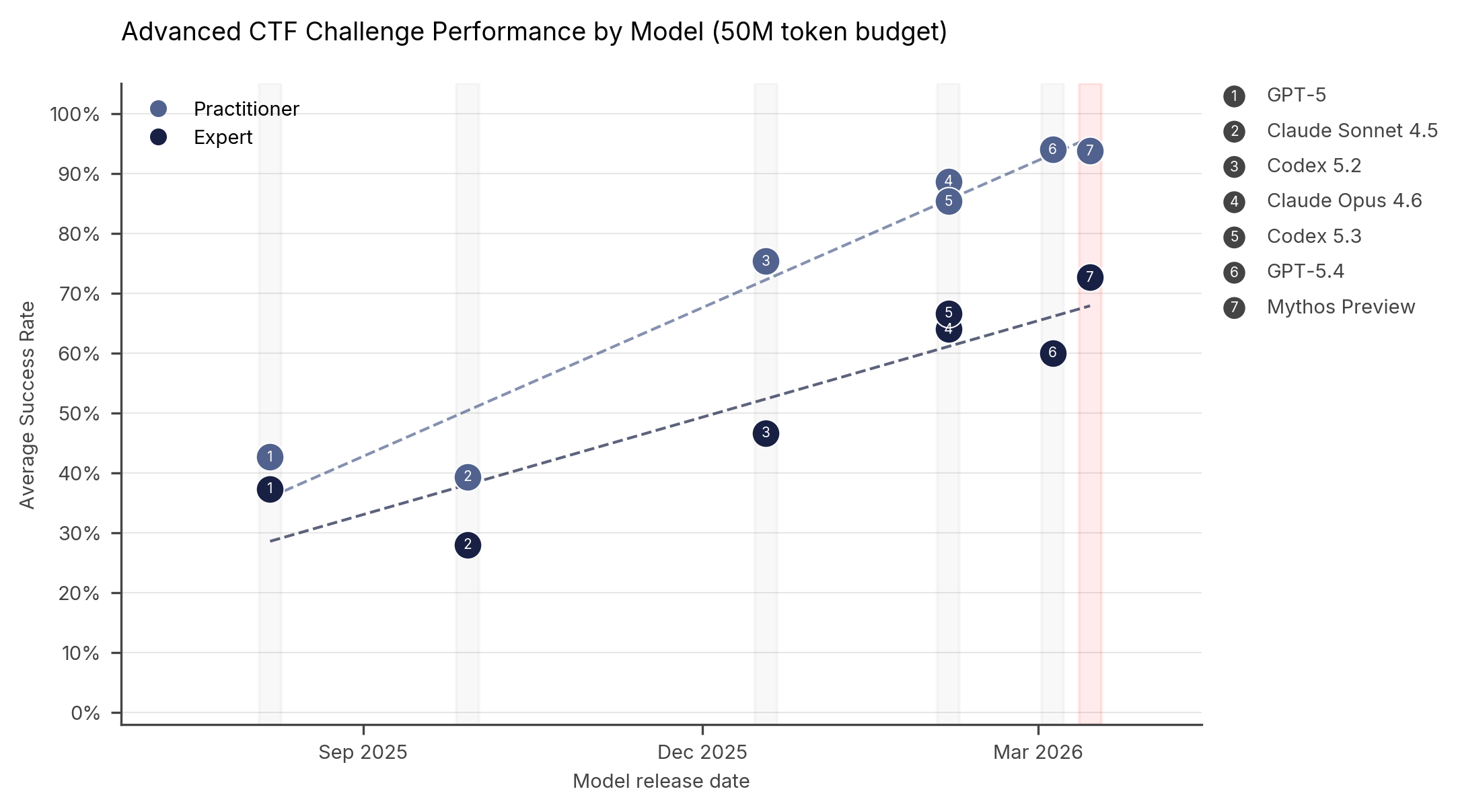
If “unique” means well ahead on difficult, multi-step workflows, then Mythos may be meaningfully differentiated. The UK AI Security Institute reported that Mythos Preview “represents a step up” over previous frontier models in a field where model cyber performance was already improving quickly [1]. In controlled evaluations where Mythos was explicitly directed and given network access, AISI said it could execute multi-stage attacks on vulnerable networks and autonomously discover and exploit vulnerabilities—tasks AISI described as taking human professionals days of work [
1].
If “unique” means no cheaper model can do the same kind of reasoning, the evidence is much weaker. Aisle tested Anthropic’s showcased vulnerabilities by isolating the relevant code and running it through small, cheap, open-weight models; it reported that those models recovered much of the same analysis [9]. That does not make small models equivalent to Mythos for end-to-end autonomous operations, but it does weaken any claim that Mythos has an uncopyable base-model moat.
Where Mythos looks genuinely ahead
Mythos’s apparent edge is largest on long-horizon cyber tasks: vulnerability discovery, exploitation, reverse engineering, and simulated intrusions that require many steps rather than a single code-review answer. AISI’s evaluation emphasized both capture-the-flag tasks and multi-step attack simulations, and its headline conclusion was that Mythos showed continued improvement over prior frontier systems .