The practical answer is narrower than a simple yes or no: DeepSeek V4 may be acceptable for low-stakes experimentation, but it should not be used for confidential, regulated, workplace, government, legal, health, financial, source-code, or personally identifying information.
The strongest evidence available here concerns DeepSeek’s broader app and service, not a fully verified safety profile for every possible “DeepSeek V4” access point. That distinction matters, because some V4-related sources describe expected or rumored release timing, while another V4 information site explicitly says it is not affiliated with DeepSeek [2][
7][
11].
The short verdict
If you are in the U.S., the sources reviewed here document government and institutional restrictions on DeepSeek, but they do not establish a blanket federal ban on ordinary private access [14][
19][
23]. That does not make it safe for sensitive use.
A reasonable default is:
| Situation | Safer answer |
|---|---|
| Casual prompts using public, non-sensitive information | Lower risk, but verify the site or app is official first. |
| Personal data, passwords, private documents, medical, legal, financial, or client information | Do not use it. |
| Work laptop, school device, contractor system, or regulated-industry environment | Do not use it unless your organization explicitly approves it. |
| Government-furnished equipment or agency-managed networks | Avoid it; some U.S. government environments have already restricted DeepSeek [ |
| Confidential engineering, source code, product plans, contracts, or trade secrets | Use an approved enterprise tool or controlled local deployment instead. |
The core privacy issue: where DeepSeek data may go
The main concern is not that DeepSeek is an AI chatbot. The concern is the data path and the legal environment around it.
NPR reported that DeepSeek sends the data it collects on Americans to servers in China, according to the company’s terms of service [13]. WIRED similarly reported that DeepSeek’s English-language privacy policy says the company stores collected information on servers located in the People’s Republic of China [
16]. The Associated Press also noted that DeepSeek’s privacy policy acknowledged storing data on servers inside China [
24].
That does not prove that any particular prompt will be misused. It does mean U.S. users should assume that anything submitted to the cloud service may be handled under cross-border data conditions. For sensitive information, that is enough to change the risk calculation.
U.S. government and workplace restrictions raise the risk
The available sources show restrictions in official settings rather than a universal U.S. consumer ban.
Reuters reported that U.S. Commerce Department bureaus broadly prohibited DeepSeek access on government-furnished equipment to help protect Commerce information systems [14]. A government-contracts analysis described NASA restrictions that barred use of DeepSeek products and services with NASA data, on government-issued devices, and through agency-managed networks [
19]. PBS also reported that House lawmakers proposed legislation to ban DeepSeek from federal devices [
23].
For workers, the practical lesson is simple: if the device, network, or data belongs to an employer, school, agency, client, or contractor program, do not treat personal access rules as enough. Organizational policy controls the risk.
Treat national-security claims carefully, but do not ignore them
CNBC, citing Reuters, reported that a senior U.S. official alleged DeepSeek was aiding China’s military and intelligence operations and had access to large volumes of Nvidia H100 chips [15]. Based on the source available here, that should be treated as an allegation by a U.S. official, not as a final public finding.
Even without relying on that allegation as proven, the privacy-policy reporting and official-device restrictions are sufficient reason to avoid DeepSeek for sensitive work [13][
14][
16][
19][
24].
Verify that “DeepSeek V4” is actually official
There is another practical problem: the “V4” label itself may not tell you enough.
Some V4-related pages in the available sources discuss expected or rumored release windows [2][
7]. A prediction-market page discusses a claimed V4 preview launch [
4]. A separate DeepSeek V4 information site says it is an unofficial hub and is not directly affiliated with DeepSeek [
11].
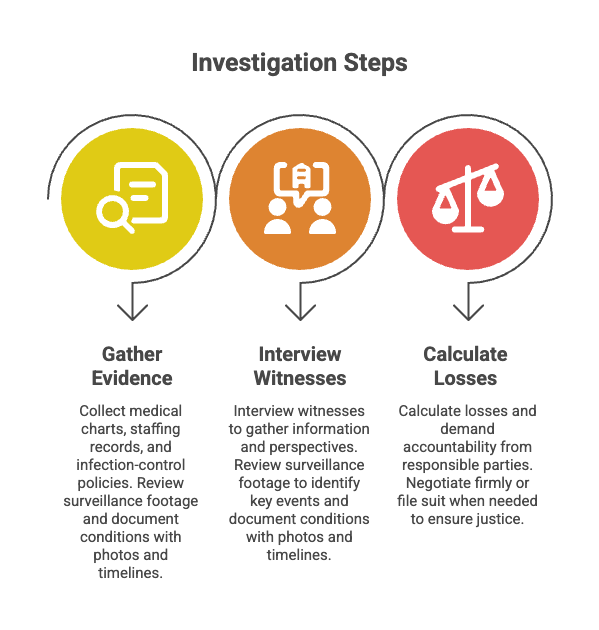
Before logging in, installing anything, or entering prompts, check:
- The exact domain and app publisher
- Whether the service is operated by DeepSeek or by a third party
- The privacy policy and data-retention terms
- Whether prompts are used for training or review
- Where data is stored or processed
- Whether your employer or agency has approved the tool
If you cannot verify those basics, do not enter anything you would not be comfortable making public.
What not to enter into DeepSeek V4
Avoid submitting or uploading:
- Passwords, API keys, tokens, private keys, or credentials
- Social Security numbers, passport numbers, addresses, phone numbers, or private messages
- Client, patient, student, employee, customer, or contractor data
- Medical, legal, tax, insurance, immigration, employment, or financial records
- Proprietary source code, internal documents, contracts, product plans, or trade secrets
- Government, defense, law-enforcement, or regulated-industry information
- Unpublished research, confidential strategy, or nonpublic business data
This is a conservative rule, but it is the right default when a cloud AI service has unresolved cross-border data-handling concerns.
When it may be acceptable
DeepSeek V4 may be reasonable for low-stakes prompts if you are using a verified official access point and the information is already public or invented. Examples include brainstorming generic ideas, summarizing public concepts, rewriting non-confidential text, or comparing model behavior with fictional test data.
Even then, reduce exposure: use a separate account if practical, avoid linking sensitive services, do not upload private files, and do not assume that deleting a chat removes every retained copy unless the official terms clearly say so.
Better choices for confidential work
For anything confidential, use a deployment with stronger controls:
- An approved enterprise AI tool covered by your organization’s privacy, retention, and security terms.
- A local model running on your own machine or controlled infrastructure, if your organization permits it.
- A vetted provider with contractual limits on retention, training use, access logging, compliance, and regional storage.
The important question is not only which model you use. It is who operates the service, where the data goes, what contract or policy applies, and whether your organization has approved it.
Bottom line
DeepSeek V4 is best treated as safe only for public, non-sensitive experimentation. The available sources do not show a blanket U.S. ban for ordinary private users, but they do show serious privacy concerns around China-based data handling and meaningful restrictions in U.S. government settings [13][
14][
16][
19][
23][
24].
If you are handling confidential, regulated, employer, government, legal, health, financial, or personal data, choose a vetted alternative instead.